GRIDNET Core 1.9.5 Release Notes — Hard Fork
Download: https://gridnet.org/GRIDNETCore.zip
And lo, the Wizards said unto the nations: Come, sit at our table, and you shall feast upon knowledge and prosper. But he who overturns our table shall hunger in darkness, and his deeds shall be laid bare before all.
Release Type: Major Hard Fork
Development Period: April 2025 — February 2026
Prior Release: GRIDNET Core 1.7.0 (April 2025)
Intermediate Releases: 1.8.6, 1.9.1, 1.9.2, 1.9.4
Foreword
GRIDNET Core has been developed with full transparency since the early 2017 — nearly every line of code conceived, implemented, debugged, and validated on YouTube LIVE, almost each and every day. This document serves as the comprehensive technical companion for investors, operators, and community members seeking a meticulous account of the work undertaken since the last release.
The 1.9.5 release represents the most architecturally ambitious cycle in GRIDNET history. What began in April 2025 with crash dump forensics, LARS autonomous deployment, and Merkle Patricia Trie investigations evolved into a ten-month odyssey that touched virtually every layer of the stack — from the lowest-level C++ memory allocators in the Merkle Patricia Trie, through the GridScript virtual machine and its compiler infrastructure, up to the browser-native Decentralized User Interface framework, and all the way to the cryptographic protocols binding them together.
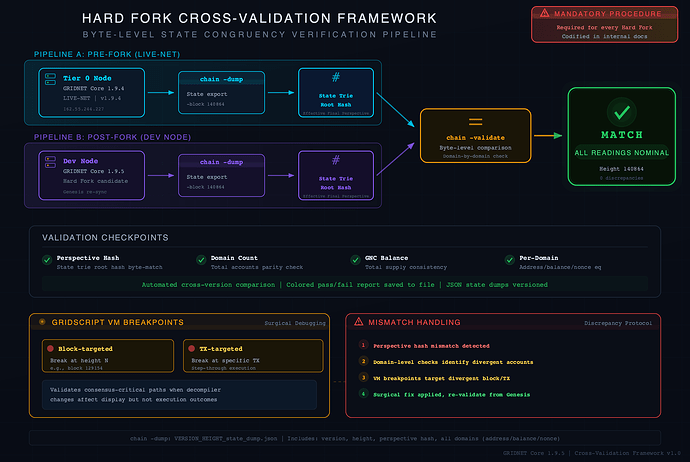
Along the way, the team discovered and patched critical security vulnerabilities within hours on live television, responded to a suspected transaction-withholding attack on Live-Net, pioneered an AI-augmented development methodology that shifted the coding-to-testing ratio to 25/75, and built cross-hard-fork validation tooling that is now mandatory for every future release — tooling that confirmed, at blockchain height 140864, byte-level congruence of the entire state trie between the pre-fork Live-Net and the post-fork candidate.
254 development days. Streamed publicly. No closed doors. This is what was built.
Critical Highlights
- Wallet UI dApp — A fully decentralized, browser-native wallet with multi-keychain management, ECC-authenticated transactions, real-time balance retrieval, PIN-lock security, AES-GCM encrypted address book, responsive design, multi-recipient value transfers, PDF receipt generation, and GLink deep-linking — all running within a single browser tab as a true GRIDNET OS UI dApp. No extensions. No server dependencies. 101% open source.
- Identity Token Registration Wizard — Fully autonomous, multi-stage identity deployment from the browser: sacrificial transaction, monitoring, DPT pre-validation, BER-encoded Identity Token creation in JavaScript, on-chain registration — zero trust in any remote node.
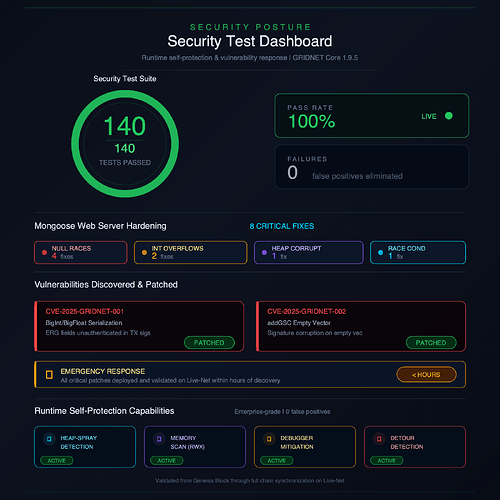
- Advanced Self-Protection Module — Enterprise-grade runtime self-protection: heap-spray detection, memory scanning, debugger mitigation, and detour injection detection — capabilities previously reserved for software suites such as Google Chrome. 140 security tests. 0 failures.
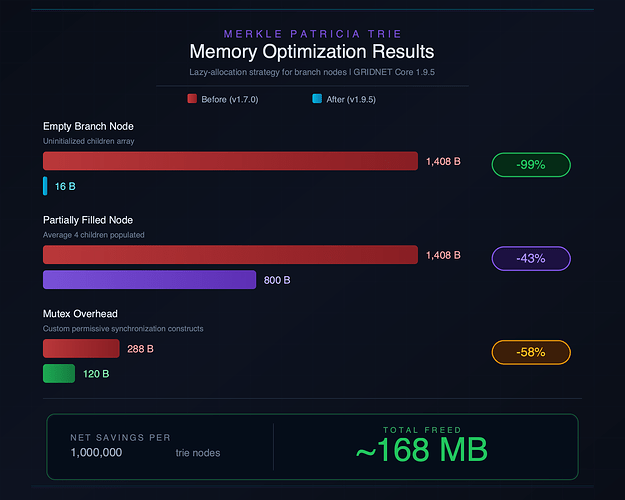
- Merkle Patricia Trie Memory Optimization — Up to 99% savings for empty branch nodes, 43% for partially filled nodes, 58% reduction in per-mutex overhead — approximately 168 MB saved per million trie nodes.
- Critical CVE Mitigations — Emergency Response Team patches for MPT rearrangement memory corruption, BigInt serialization vulnerabilities, and null-pointer dereferences — all validated on Live-Net within hours.
- Multi-Dimensional Token Pools & Off-Chain Payments — End-to-end off-chain payment pipeline: Token Pool registration, Transmission Token generation/import/cash-out, double-spend prevention, and deterministic seed derivation from master key.
- GridScript ACID Commitment Overhaul — Detached VM thread execution, system-mode authentication, ephemeral sandbox execution with deferred authentication, and cross-UI-dApp synchronization.
- In-Browser GridScript Compiler — Transactions compiled, signed, and dispatched entirely from within the browser — passing all pre-validation tests on GRIDNET Core including code integrity and ECC signature verification.
- GLink Deep-Linking System — URL-triggered multi-stage processing: GRIDNET OS boot, user authentication, UI dApp launch, view activation, and form data population — all from a single link.
- Hard Fork On-Chain Metadata — Explicit transaction type metadata stored on-chain, eliminating the need to parse Turing-complete GridScript bytecode. Millisecond-speed blockchain search via the new
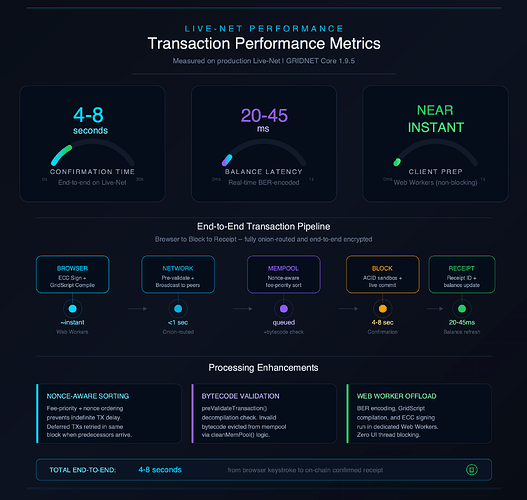
mkfilterGridScript command. - Transaction Processing Enhancements — Nonce-aware fee-priority sorting, mempool pre-validation, invalid bytecode detection, and 4–8 second confirmation times on Live-Net.
- AI-Augmented Development Pipeline — Anthropic AI integration for root cause analysis, code review, cross-platform compiler validation, and crash dump analysis — shifting to a 75% testing / 25% coding workflow.
- Mongoose Web Server Hardening — Eight critical fixes to the embedded Mongoose HTTP/WebSocket server: NULL pointer races, integer overflows, heap corruption, and race conditions.
- Cross-Hard-Fork Validation Framework —
chain -dumpandchain -validatecommands for byte-level state trie comparison between pre-fork and post-fork nodes. All readings nominal at height 140864. Now mandatory for every Hard Fork Procedure. - Phantom Leader Mode — Sandboxed transaction simulation enabling any Operator to preview expected mempool outcomes without affecting live consensus — born from response to a suspected withholding attack.
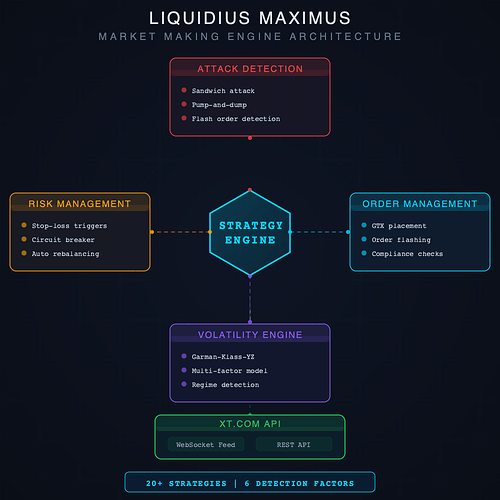
- Liquidius Maximus Market Making Engine — Comprehensive Python-based high-frequency trading platform with 20+ strategies, Qt6 flame-chart profiler, Garman-Klass-Yang-Zhang volatility estimation, sandwich/pump-and-dump detection with autonomous mitigation, self-learning defense adaptation, flashing order book module, and GTX post-only order placement — purpose-built for GNC/USDT liquidity provision. To be released as entirely open source following the termination of Xt.com cooperation due to documented predatory market manipulation.
- LARS Autonomous Update Engine — LARS evolved from a crash reporter into a fully autonomous deployment system: self-updating GRIDNET Core installations, MSI installer extensions, pre-flight validation suites, blockchain height stall monitoring, crash-loop resilience, GPU diagnostics, runtime DLL introspection, and VC++ Runtime management.
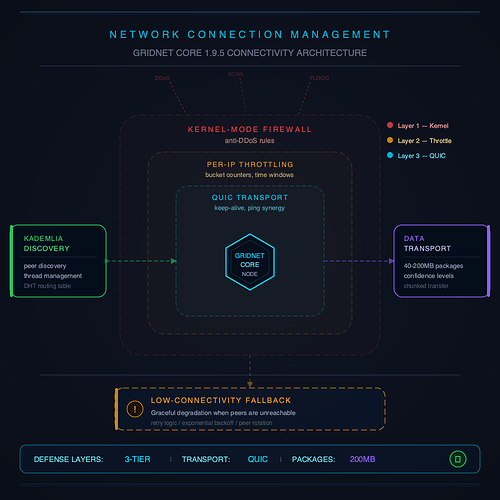
- Network Connection Hardening — Per-IP connection throttling, low-connectivity fallback mode, kernel-mode firewall integration, QUIC keep-alive tuning, application/transport-layer ping synergy, and maximum data package size extended from 40 MB to 200 MB for growing blockchain synchronization demands.
- Emergency CVE Campaign Response — GridScript meta-data generation attack vector, Kademlia peer discovery exploit, network black-hole attack, ERG limit exploitation, SEH disabling attack campaign, and WebSocket data fuzzing attack — all discovered, patched, and deployed via LARS within hours.
Wallet UI dApp — A Fully Decentralized Browser-Native Wallet
Every blockchain project has a wallet. Almost none of them are truly decentralized. MetaMask runs as a browser extension with closed-source components. Hardware wallet interfaces depend on manufacturer servers. Mobile wallets are compiled binaries whose source you never see.
The GRIDNET Wallet UI dApp is different by construction. It is delivered on-chain as source code, decompiled on-the-fly by the user’s browser, and executed within GRIDNET OS process isolation inside a single browser tab. There are no binaries to trust, no extension permissions to grant, no server-side dependencies to rely on. The code is open, verifiable, and self-contained — and any developer can fork it, modify it, and deploy their own version on-chain.
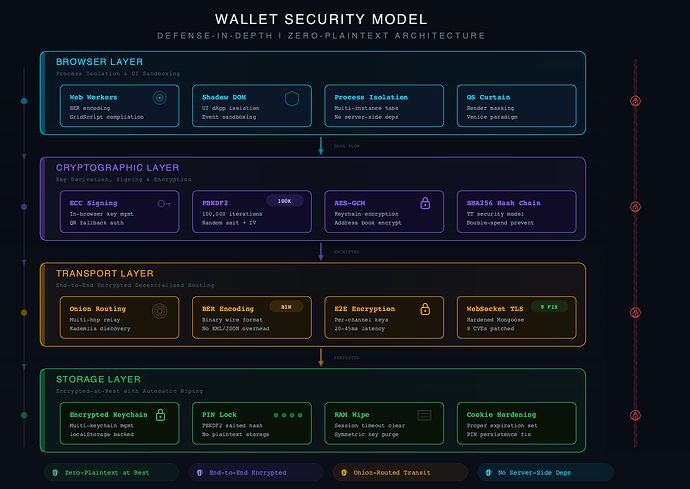
Building a wallet this way is harder than every alternative. It means implementing ECC cryptography in JavaScript. It means managing keychains entirely in-browser. It means serializing every data structure to BER format and routing every message through onion-encrypted WebSocket channels. But the result is a wallet whose security model is mathematically verifiable by anyone who can read JavaScript — because all of it is right there in the source code, served from the blockchain itself.
Core Capabilities
- Multi-keychain architecture — multiple keychains, each holding multiple sub-identities, with animated fold/unfold transitions and single-tap identity switching that propagates system-wide across all running UI dApps.
- Real-time balance and history — data flows onion-routed, BER-encoded, and end-to-end encrypted over WebSocket channels. Balance update latency: 20–45 ms on local network.
- Value transfer with dynamic cost estimation — slider-based transfer UI with real-time fee calculation, multi-recipient support with drag-and-drop ordering, and mempool-aware next-nonce prediction. Custom draggable library ensures slider interaction doesn’t trigger container rearrangement. Dynamic Pool Tracking creates a zero-sum allocation model where adjusting one recipient instantly updates all others.
- PIN-lock and keychain encryption — PBKDF2-derived (100,000 iterations) salted PIN hashing replaces prior plaintext storage. AES-GCM encrypted keychain data stores with automatic lock/unlock on timeout. Symmetric keys wiped from RAM upon session timeout.
- Stored recipients with AES-GCM encryption — encrypted-at-rest address book with zero plaintext persistence when locked, quick-save from send view, and one-click auto-fill.
- PDF receipt generation — downloadable Value Transfer Confirmation receipts generated directly from the wallet, available both pre-confirmation (proof of submission) and post-confirmation (proof of settlement).
- Responsive design — Exodus-class visual aesthetics adapted from narrow smartphone to ultra-wide desktop, with dynamic element repositioning, conditionally hidden logo, and cyberpunk hover/drag effects.
- Initial development (April–May 2025) — tabbing mechanics, dashboard views, Shadow-DOM component architecture, and key-chain management JavaScript API enabling all
KeyChainGridScript command functionalities from JavaScript. - In-browser wallet address generation — all custom cryptographic primitives (including RIPEMD-160) ported from C++ to JavaScript/ECMA6, enabling fully headless in-browser key derivation.
- Headless authentication — asynchronous data-request pipeline for symmetric password prompts with full-screen secure-desktop-style passphrase entry, promise-based resolution, and automatic timeout.
Transaction Commitment Architecture
The Wallet UI dApp pioneered a new architecture for GridScript code commitment from the browser — a pipeline that did not exist before this release:
![Transaction Commitment Flow Architecture Diagram]](upload://nmDnluuGs3EvmnWmTUS0w45a42L.png)
- JavaScript ECMA6 formulates GridScript instruction sequences
- Web Workers perform BER encoding, GridScript compilation, and ECC signing — off the main thread
- Compiled bytecode is dispatched through onion-routed, encrypted WebSocket channels
- GRIDNET Core nodes receive, pre-validate, and broadcast to the network
- Operators include validated transactions in newly formed Data Blocks
- Results flow back through the same onion-routed channel to the specific UI dApp instance
A critical architectural breakthrough was the introduction of System-mode commitment — enabling headless commits without requiring a per-process handle. A single password prompt per session, with graceful fallback to QR code authentication when the KeyChainManager cannot fulfill signing requests locally.
The commitment pipeline also introduced progressive commit monitoring with exponential fallback: initial 3-second check, then retries at 5, 10, and 15-second intervals — replacing the brittle fire-and-forget model of previous releases.
GridScript VM as a Decentralized Service-Oriented Architecture
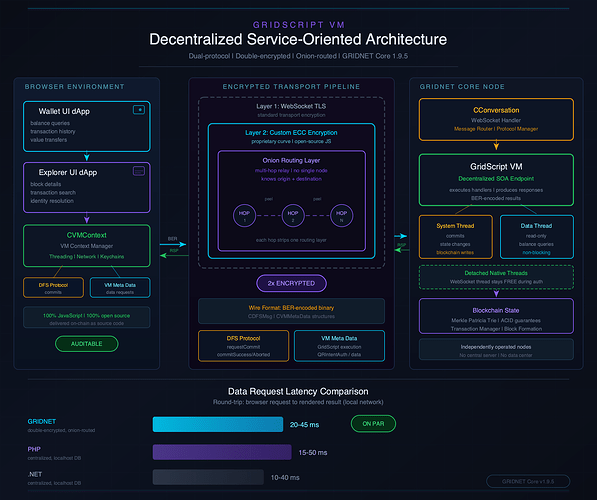
Stop and consider what is actually happening when a user opens the Wallet UI dApp or the Blockchain Explorer in their browser.
Every balance displayed. Every transaction listed. Every block detail rendered. Every identity resolved. None of it comes from a traditional server. There is no PHP backend. There is no .NET API. There is no REST endpoint hosted in a data center. Every single piece of data the user sees on screen is retrieved through GridScript code executing on remote GRIDNET Core nodes — decentralized machines operated independently across the network.
This is not a theoretical capability. It is production reality. Both the Wallet UI dApp and the Blockchain Explorer UI dApp — the two flagship applications shipped with this release — operate entirely on this architecture. When the Wallet queries an account balance, it constructs a GridScript data request in JavaScript, BER-encodes it, wraps it in custom ECC encryption, sends it through a TLS-secured WebSocket, and routes it through GRIDNET’s onion-routing layer to reach a Core node. That node executes the corresponding GridScript handler, produces a BER-encoded response, and sends it back through the same double-encrypted, onion-routed channel. The browser decodes the response and renders it. The user sees a number on screen and has no idea that what just happened bears no resemblance to a conventional HTTP request-response cycle.
The encryption model deserves emphasis: every data request travels through two independent encryption layers. The outer layer is standard WebSocket TLS — the same transport security used by every modern web application. The inner layer is GRIDNET’s own ECC-based encryption, applied at the application level before the data ever reaches the WebSocket. An attacker who somehow compromised the TLS layer would still face a second, entirely separate cryptographic barrier. And because the inner encryption is implemented in JavaScript — delivered as source code from the blockchain itself — it is fully auditable. There are no compiled binaries, no opaque cryptographic libraries, no trust-us-it-works black boxes. Every encryption operation can be read, verified, and validated by anyone with a browser’s developer tools.
The onion routing adds a third dimension of protection: even if both encryption layers were somehow breached, the multi-hop relay architecture ensures that no single node in the network knows both the origin and destination of any given request. The request hops through intermediate nodes, each peeling one layer of routing information, before reaching its destination. Privacy is not a feature bolted on after the fact — it is woven into the transport fabric.
What makes this genuinely remarkable is the performance. The measured balance update latency — the round-trip time from browser request to rendered result — is 20–45 milliseconds on a local network. That is not a typo. A double-encrypted, onion-routed, BER-encoded request to a GridScript virtual machine running on a remote decentralized node, with the response traveling back through the same pipeline, completes in under 50 milliseconds. This is on par with — and in many cases faster than — conventional centralized web frameworks like PHP, Ruby on Rails, or ASP.NET querying a local database over localhost.
The GridScript VM has effectively become a decentralized SOA endpoint. Traditional Service-Oriented Architectures rely on centralized servers exposing well-defined APIs. GRIDNET has achieved the same pattern — well-defined service interfaces, request-response semantics, structured data encoding — but with the servers replaced by a decentralized network of independently operated nodes, and the communication channel replaced by an onion-routed, double-encrypted, censorship-resistant transport layer.
This is what replaces traditional server-side backends. Not partially. Not as a proof of concept. In production, today, serving real users on Live-Net.
Identity Token Registration Wizard
Registering an identity on a blockchain should not require downloading a separate binary, trusting a third-party service, or understanding cryptographic primitives. The Identity Token Registration Wizard makes on-chain identity deployment a guided, multi-stage process — executed entirely from the browser.
Every blockchain platform that supports on-chain identities eventually confronts the same question: how do you make identity registration accessible without compromising sovereignty? Most projects punt — they build a centralized web portal, or they require users to install CLI tools and paste hex-encoded strings into a terminal. The GRIDNET approach was to build a wizard that handles the full complexity of multi-stage blockchain commitment autonomously, while keeping the user informed at every step. The result is a process that is technically rigorous and genuinely usable — no cryptography degree required.
The wizard handles a complex sequence autonomously:
- Sacrificial transaction — the wallet compiles GridScript bytecode, signs via custom ECC, broadcasts the sacrificial transaction, and monitors the blockchain for confirmation with real-time progress updates.
- Automatic progression — once confirmed, the UI auto-transitions to the next stage. No clicks required.
- Historical transaction detection — the wizard retrieves previously committed sacrificial transactions, enabling cross-device workflow continuity (start on one machine, finish on another).
- DPT pre-validation — before committing the Identity Token to the blockchain, the wizard executes the target GridScript in a sandboxed Decentralized Processing Thread. Only on confirmed success does it proceed.
- Identity Token creation — full
CIdentityTokencreation matching the C++ implementation, BER serialization, base58check encoding, all generated in JavaScript. - On-chain registration — the final transaction is compiled, authenticated, and broadcast.
Two deployment modes are supported: local compilation (zero-trust, everything happens in the browser) and DPT mode (remote compilation, QR-code authenticated through the mobile app). The bambino state-domain was the first identity successfully registered through this wizard on Live-Net — entirely autonomously.
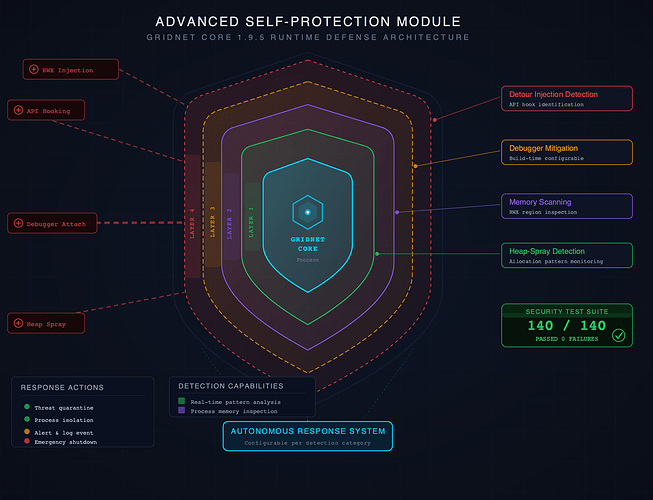
Advanced Self-Protection Module
Most blockchain software trusts the operating system to protect it. GRIDNET Core does not make that assumption.
A blockchain node is not a web app that can be restarted if something goes wrong. It holds private keys. It processes value transfers. It participates in consensus where a single corrupted state transition can fork an entire network. The threat model is not hypothetical — memory injection attacks, DLL hooking, debugger-assisted key extraction: these are real techniques used against real financial software. The Advanced Self-Protection Module was built with the conviction that a blockchain node should defend itself with the same intensity that browsers like Google Chrome bring to protecting a sandboxed tab. The protections implemented here are found in fewer than a handful of software suites globally, and for software that may hold value and process financial transactions, this level of paranoia is not excessive; it is appropriate.
- Heap-spray detection — real-time monitoring of memory allocation patterns to detect heap-spraying attack techniques. False positive elimination refined through iterative testing against Visual Studio debug heap patterns, achieving 0 false positives after calibration. The system flags suspicious allocation patterns and can trigger autonomous response.
- Memory scanning — inspection of process memory regions for suspicious RWX (Read-Write-Execute) allocations. Legitimate code sections (e.g.,
__enc$textbss$beginfrom Visual Studio runtime) are properly excluded. Any unexpected RWX region triggers investigation. - Debugger mitigation — configurable build-time options for debugger detection and countermeasures. An attacker who attaches a debugger to a running GRIDNET Core instance faces detection and response.
- Detour injection detection — identification of API hooking and function detour injection attempts. This protects against DLL injection attacks that modify function behavior at runtime.
- Automatic response mechanics — autonomous threat response capabilities configurable per detection category. The node can respond to threats without human intervention.
- Security test suite — 140 dedicated security tests with 100% pass rate, evaluated from Genesis Block synchronization through full chain validation. Every test passed. Zero failures.
- Runtime SEH Integrity Verification — inline-assembly-based runtime self-diagnostic checks detecting whether Structured Exception Handling has been disabled or overridden by hostile actors, with obfuscated assembly to resist binary patching.
- Kernel-Mode Aided Self-Protection — user-mode Win32 API module unloading with kernel-mode escalation for forceful neutralization. Initializes early in boot sequence.
- IAT/EAT Hook & Deroute Detection — scanning of all loaded modules for Import Address Table and Export Address Table hooks, inline patches, and derouted function pointers.
- ETW-Based Process & Thread Monitoring — Windows Event Tracing with custom private session for real-time detection of injected DLLs, rogue threads, and process-level intrusions.
- AtomBombing / APC Injection Detection — detection for the AtomBombing code-injection technique exploiting Windows atom tables and Asynchronous Procedure Calls.
- Custom PEB/TEB Structure Definitions — Process Environment Block and Thread Environment Block structures incorporating undocumented Windows internal fields.
GridScript & Execution Enhancements
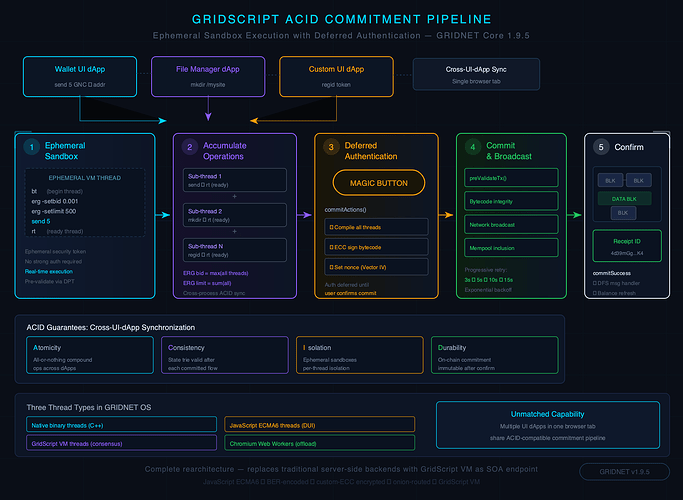
ACID-Compatible Flow Processing
GridScript is a Turing-complete virtual machine. Running Turing-complete code inside a consensus-critical blockchain kernel is inherently dangerous — a single incorrect state transition can fork the network. The ACID overhaul addresses this by introducing proper transactional semantics borrowed from database theory.
The challenge that drove this work was deceptively simple on the surface: let browser-based UI dApps execute GridScript code, accumulate changes, and commit them atomically. In practice, this meant solving a problem that database engineers have studied for decades — how do you let multiple concurrent actors modify shared state without corruption? The answer, as it has been since the 1980s, is ACID: Atomicity, Consistency, Isolation, Durability. What is new here is applying those guarantees not to rows in a database, but to state transitions inside a decentralized virtual machine running across an adversarial network.
- Ephemeral sandbox execution with deferred authentication — UI dApps execute GridScript code in real-time sandboxes, accumulate operations across multiple threads, and defer cryptographic authentication to the commitment phase. Think of it as a database transaction: changes are tentative until
COMMIT. - Cross-UI-dApp synchronization — ACID-compatible coordination of GridScript commitment across multiple applications running in the same browser tab. Two dApps can modify state in the same atomic operation — a capability unmatched in competing blockchain platforms.
- ERG command additions — new
ERGGridScript commands (setbid,setlimit) enabling UI dApps to programmatically configure execution resource allocation (gas equivalent) parameters. Two new VM special registers store pre-validated ERG amounts, eliminating user prompts when values are already known. chain -bfcommand — Operators can query real-time status of key-block and data-block formation.chain -phantom on/off— toggles Phantom Leader Mode from the GridScript terminal.
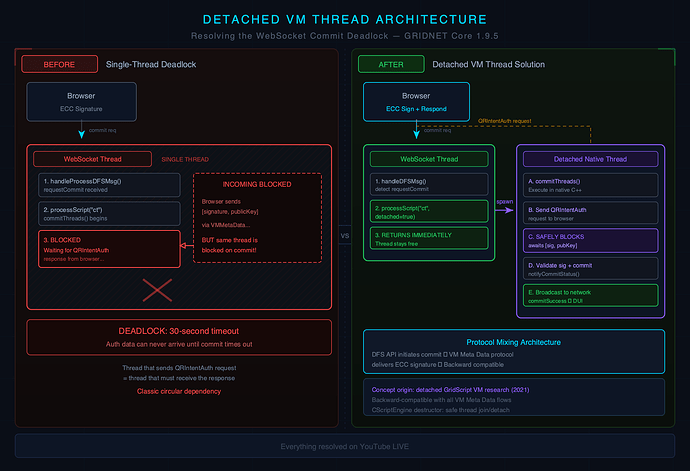
Detached VM Thread Architecture
During the implementation of browser-based transaction commitment, the team encountered a deadlock that would have been invisible in testing but fatal in production:
The WebSocket thread handling commit requests was the same thread required to receive authentication responses. When the thread blocked waiting for an ECC signature from the browser, it could never receive that signature — because the incoming data had to arrive through the same blocked thread.
This is the kind of bug that does not surface in unit tests. It does not appear in staging environments with low concurrency. It waits for production traffic, for the exact moment when a user’s wallet is mid-commit and the system seizes.
The solution drew on research from 2021: detached GridScript VM threads. Commit operations now spawn a native C++ thread that blocks independently while the WebSocket thread returns immediately, remaining responsive for incoming authentication data. The detached thread safely awaits the ECC signature, validates it, commits the transaction, and calls notifyCommitStatus(). Backward-compatible with all existing VM Meta Data protocol flows.
In-Browser GridScript Compiler
A milestone that seemed distant at the start of the release cycle: the browser can now compile, sign, and dispatch GridScript bytecode entirely on its own — without any assistance from a remote GRIDNET Core node for compilation.
This was achieved through a massive porting effort — wrapping the CTransaction C++ nested BER-encoded data structure (3-4 levels of inheritance) for JavaScript production. AI agents were deployed to compare C++ and JavaScript implementations, continuously generating unit tests with test vectors and correlating results until the JavaScript compiler output matched the C++ reference implementation byte-for-byte.
The security implications are profound: the browser becomes the sole trusted entity. No remote node compilation. No blind trust in bytecode received from the network. The user’s browser compiles from source, signs with a local private key, and dispatches the authenticated package. This is the logical conclusion of a design philosophy that treats every external dependency as a potential attack surface — and eliminates them one by one until the only thing the user needs to trust is the code running in their own browser.
GridScript Decompiler Fix
Investigation revealed a bug in the GridScript decompiler where the -r (recipient) switch was not properly decompiled in Transmission Token cash-out instructions. Extensive cross-validation through GridScript VM-level breakpoints confirmed the bug affected display only — the kernel-mode execution path correctly inferred recipients from the data stack. The Effective Final Perspective (state trie root hash) was congruent between fixed and unfixed nodes, confirming no backwards compatibility layer was required.
- ERG Control Bypass During Exception Handling — ERG checks and deduction logic now disabled during GridScript exception-handling sequences, patching a vulnerability where low ERG limits caused fatal double-exception termination.
- GridScript VM Exception Processing Hardening — extensively revised exception processing across multiple code paths with reinforced general exception handlers around value-transfer API execution, block formation, and chain-proof instantiation.
Merkle Patricia Trie — Memory & Stability
The Merkle Patricia Trie is the data structure at the heart of every account, every balance, every identity on GRIDNET. Every node in the network maintains a copy. Every byte of overhead per trie node is multiplied by millions of nodes across thousands of operators. Memory optimization here is not premature — it is economically significant.
But memory was only the beginning of what this release cycle demanded. What started as a careful optimization effort turned into months of deep debugging when live-net conditions exposed a critical memory corruption vulnerability and multi-threaded race conditions that only surfaced under real-world bootstrap loads. The trie is the single most exercised data structure in GRIDNET Core — every block touches it, every transaction modifies it, every new operator rearranges it. Making it smaller was the plan. Making it survive everything the network could throw at it became the mission.
Memory Optimization
The insight was simple: most branch nodes in a Merkle Patricia Trie are empty or nearly empty. Allocating a full 16-child array (plus hashes, descriptors, and synchronization primitives) for every node — including nodes with zero children — is wasteful.
The solution: lazy allocation.
| State | Before | After | Savings |
|---|---|---|---|
| Empty branch node | ~1,408 bytes | ~16 bytes | ~1,392 bytes (99%) |
| Partially filled (avg 4 children) | ~1,408 bytes | ~800 bytes | ~608 bytes (43%) |
| Fully populated | ~1,408 bytes | ~1,408 bytes | 0 bytes |
All 12+ accessors (getMemberHash, setMemberHash, mMemberDescriptor, setMemberDescriptor, recalculateHashes, setAllMemberHashes, setMember, clear, copy constructor, operator=, prepare for serialization and deserialization) updated with null-safe lazy initialization. Nothing allocates until something needs to be stored.
Additionally, custom permissive synchronization constructs were optimized from ~288 bytes to ~120 bytes per mutex when authorization is unused — a 58% reduction. For a trie with one million nodes, this alone saves approximately 168 MB.
Critical Vulnerability: MPT Rearrangement Memory Corruption
On November 10, 2025, an Emergency Response was triggered on YouTube LIVE.
A newly joined Operator had — by random chance — self-assigned a state-domain identifier located immediately adjacent to the Treasury account in the Merkle Patricia Trie. When the block-reward processing (Flow/ACID layer) created the Operator’s account, the trie rearranged its nodes. The Treasury account was relocated to a new memory address — but the ACID layer still held a pointer to the old address. Memory corruption.
The triggering Operator was identified as 1JWvujzgQvyAMdzAjh1eBA9vCycWcpvZGP at block height 129154. Emergency patches were deployed and validated within hours. A similar vulnerability was identified in the transaction processing path where target account creation could displace Treasury nodes — also patched.
Multi-Threaded Processing Fix
A crash occurring during initial bootstrap — triggered during multi-threaded validation of the longest chain-proof delivered from the network — was traced to the multi-threaded Merkle Patricia Trie processing path and resolved.
- Multi-Tier Meta-Data Cache Synchronization — massive synchronization overhaul after LARS reports revealed race conditions where multiple threads (up to four simultaneously) fired meta-data cache updates against the same MPT instance. Fixes included RAII-managed synchronization constructs and proper isolation guarantees.
- Node-Level Critical Sections via Dynamic Mutex Map — per-node critical section mechanism using a dynamic map of mutexes keyed by sub-node hash, protecting availability checks and lazy instantiation during multi-threaded traversal.
- BER Data-Type Pre-Sensing — custom low-level code performing manual BER data-type sensing prior to Botan library decoding, bypassing exception-heavy handling for ten-fold or greater performance improvement in meta-data preparation speed.
Emergency Response: CVE Discoveries & Rapid Mitigation
Security vulnerabilities are inevitable. What defines a project is how it responds to them — how fast, how transparently, and how thoroughly. The 1.9.5 development cycle tested that response capability repeatedly. Multiple security vulnerabilities were discovered, disclosed, and patched — often within hours, always on camera. Every fix described below was developed, deployed, and validated on YouTube LIVE streams, with the full debugging process visible to anyone watching. No closed-door patches, no silent updates, no “we’ll get to it next quarter.” When something broke, it was fixed in front of the world.
CVE-2025-GRIDNET-001: BigInt Serialization
During the development of the in-browser GridScript compiler, a bug was found not in JavaScript — but in the C++ code itself. The addBigInt(), addBigFloat(), and addBigSInt() methods in the data concatenator utility copied from &mInternalTemp[0] instead of bytes.data() and failed to increment mOffset. The result: ERG Price/Limit fields were not properly authenticated in transaction signatures.
Impact: Critical. Affected transaction versions v1 through v2. Fixed with dual implementations — a corrected version and a bug-compatible version for backward chain processing.
CVE-2025-GRIDNET-002: Empty Vector Serialization
The addGSC(std::vector<uint8_t> vec) method, when receiving an empty vector, failed to increment mOffset after adding an 8-byte zero value. Active usage in Tools.cpp:5113 (sourcePubKey) and identitytoken.cpp meant this could corrupt signatures silently.
Both CVEs were patched, propagated to JavaScript and mobile app codebases, and validated through full Genesis Block synchronization — Merkle Patricia State Trie roots nominal at all tested heights.
Null-Pointer Dereference (January 2026)
A null-pointer dereference introduced on June 6, 2025 went undetected for seven months. The trigger: any transaction broadcast with an ERG limit below 1000 would crash any node on Live-Net. The attacker was identified through full memory dump analysis as… the team’s own Wallet UI dApp under development.
Patched and released as GRIDNET Core 1.9.4 within hours.
What follows is a selection of additional attack vectors discovered and neutralized during the 1.9.5 cycle. Each of these was a real incident — identified through LARS automated reporting, live-net monitoring, or direct adversarial probing — and each was resolved with targeted hardening rather than broad workarounds.
- GridScript Meta-Data Generation Attack Vector — a deliberately malformed GridScript instruction sequence discovered via LARS reports caused crashes during meta-data generation despite the transaction being correctly rejected on-chain. Emergency Response Team deployed a vaccine within 8 hours.
- Kademlia Peer Discovery Exploit — spoofed ICMP Port Unreachable datagrams disrupted UDP-based connectivity. Transport layer hardened to throw only on fatal occasions, with maximum reported neighbour counts capped to prevent DoS amplification.
- Network Black-Hole Attack — excessive advertisement of chain-proofs enabling node isolation was patched with propagation controls limiting chain-proof advertisement frequency.
- ERG Limit Exploitation Attack — attackers submitted transactions with extremely low ERG limits causing fatal double-exception crashes during GridScript execution. Hot Fix GRIDNET Core 1.6.8 deployed.
- SEH Disabling Attack Campaign — coordinated campaign where hostile actors ran GRIDNET Core with altered executables disabling Structured Exception Handling. Runtime SEH integrity verification deployed as countermeasure.
- WebSocket Data Fuzzing Attack — protocol-mismatched data dispatched to Tier 0 WebSocket endpoints causing crashes. DUI service handlers hardened against data-fuzzing vectors.
Transaction Processing & Mempool Management
Transaction processing is where theory meets production. A mempool that doesn’t sort properly delays legitimate transactions. A pre-validation step that misses invalid bytecode wastes operator resources. A nonce gap that isn’t handled correctly means users wait forever.
These are the kinds of problems that don’t show up in whitepapers or architecture diagrams. They show up when real users submit real transactions and something doesn’t work the way it should. Every fix below came from observing actual behavior on Live-Net — transactions that sat in mempools longer than they should have, status labels that confused users, cleanup routines that silently stopped running. The goal was straightforward: make transactions flow through the system the way users expect them to, without surprises.
- Nonce-aware fee-priority sorting — mempool transactions are now sorted considering both fee priority and nonce ordering. Without this, a high-fee transaction with nonce N+1 would be selected before nonce N, causing it to be deferred indefinitely — a subtle bug that only manifests under specific ordering conditions.
- Invalid bytecode detection —
preValidateTransaction()now performs bytecode decompilation checks. A newinvalidBytecoderesult type triggers mempool eviction viacleanMemPool(). Transactions that can never be valid are no longer kept around hoping they’ll become valid. - Pre-validation status tracking — new
receivedenum value (15) replaces the misleading defaultinvalidstatus shown before pre-validation completes. Users no longer see their transaction labeled “invalid” during the 100ms before validation finishes. - Retry deferred transactions — transactions deferred due to nonce gaps are now retried within the same block when preceding transactions arrive. Previously, these would wait for the next block formation cycle.
- Mempool cleanup fix — a recent security addition had inadvertently disabled mempool cleanup on nodes with block formation disabled (dev-nodes), preventing transaction pre-validation entirely. A subtle regression that could have gone unnoticed for months.
- Confirmation times — demonstrated 4–8 second confirmation times on Live-Net, with Web Worker-based compilation and signing enabling near-instant client-side preparation.
Mongoose Web Server Hardening
The Mongoose HTTP/WebSocket library is the front door to GRIDNET Core. Every WebSocket connection, every HTTP request, every Decentralized User Interface session — all of it enters through this single library. That makes it the highest-value target in the entire stack. A buffer overflow here does not just crash a web server; it potentially compromises a blockchain node. This is why GRIDNET Core maintains its own internal fork of Mongoose, hardened far beyond the upstream version through both automated pen-testing and meticulous manual code review.
During the 1.9.5 cycle, the team identified and fixed eight critical issues — the kind of low-level memory safety bugs that do not show up in normal operation but become devastating under adversarial conditions. Race conditions in buffer management. Integer overflows in WebSocket frame processing. Heap corruption from a seemingly innocuous memory-zeroing operation. Each one was a potential attack vector; each one is now closed.
| Issue | Location | Root Cause |
|---|---|---|
| NULL pointer race in resize (expansion) | mongoose.cpp:1864-1883 | Concurrent access during buffer growth |
| NULL pointer race in resize (free) | mongoose.cpp:1812-1822 | Use-after-free in buffer deallocation |
| NULL pointer race in mg_iobuf_add | mongoose.cpp:2083-2090 | Missing synchronization in buffer append |
| NULL pointer race in mg_iobuf_del | mongoose.cpp:2192-2200 | Missing synchronization in buffer delete |
| Integer overflow in mg_ws_mask | mongoose.cpp:5321-5326 | Arithmetic overflow in WebSocket masking |
| Integer overflow in mg_ws_wrap | mongoose.cpp:5527-5540 | Arithmetic overflow in frame wrapping |
| Heap corruption from zeromem | mongoose.cpp:1898, 1822 | Zeroing memory after reallocation |
| Race condition on c->send buffer | websocket.cpp | Unsynchronized concurrent writes |
Post-fix automated pen-testing confirmed: upgrades to internal WebSocket mechanics exhibit complete resilience to DOS and data fuzzing attacks. The front door is reinforced.
- BER Encoding Validation Overhaul — custom BER encoding validation heuristics external to Botan library, including manual length-field checks. Increased BER length-field allowance from 4 bytes to 5 bytes with additional reasonable-size checks.
Multi-Dimensional Token Pools & Off-Chain Payments
On-chain transactions are permanent, transparent, and slow. Off-chain payments are instant, private, and cheap. Both have a place — but until now, GRIDNET only had the on-chain path. The 1.9.5 release cycle delivers the first end-to-end off-chain payment pipeline operating through the Wallet UI dApp, closing that gap and giving users a real choice between settlement guarantees and transaction speed.
The mechanism behind it is elegant in its simplicity. Multi-Dimensional Token Pools are reverse hash-chain constructs — multiple reverse hash-chains running in parallel (hence “multi-dimensional”). Each chain link is a Transmission Token that can be given to a recipient and cashed out on-chain. The hash chain is one-way: given token N, you can verify it leads to the pool root, but you cannot derive token N+1. Double-spend prevention is built into the protocol — cashing out the same token twice fails even in sandbox mode. No external validation service. No trusted third party. Just math.
- Token Pool registration — GridScript bytecode compiled in browser Web Workers, ECC-authenticated, and committed to blockchain. Token Pool generation potentially involves millions of hashing operations, offloaded to Web Workers with real-time progress feed and time-remaining estimation.
- Deterministic seed derivation — Token Pool seeds can be deterministically derived from the keychain master private key using SHA256/HMAC, eliminating the need for local storage of pool-specific secrets. Double SHA256 operations ensure cryptographic separation between sub-identities and payment constructs.
- Token Pool enumeration — the Wallet retrieves registered pools through the Decentralized File System API with async refresh.
- Transmission Token cash-out — reverse hash chain verification with SHA256-based security. Dual-mode architecture: user-mode
xTTprovides argument validation, kernel-modexTTextakes arguments directly from the GridScript data stack. - ECC-locked verification — two-tier public key verification: primary through on-chain Identity Token, fallback through Token Pool’s stored public key.
- Bearer vs. targeted tokens — bearer tokens are cashable by anyone; targeted tokens are locked to a specific recipient.
GLink Deep-Linking System
A URL should be able to do more than open a webpage. On the traditional web, deep links are an afterthought — bolted on through query parameters that break when the frontend changes. In GRIDNET OS, deep linking is a first-class system primitive. A single GLink URL can orchestrate a complete multi-stage interaction, taking a user from cold start to a fully populated application view in one click:
- GRIDNET OS boots in a browser tab
- User authenticates (QR code or in-browser keychain)
- A specific UI dApp launches (e.g., Wallet, Blockchain Explorer)
- A particular view activates (e.g., Send tab, Block Details)
- Form data auto-populates as encoded in the GLink
GLinks support Action IDs and associated data fields, enabling target UI dApps to interpret and act on link data contextually. The processing is fully asynchronous and event-driven — no hard-coded timeouts. UI dApps notify the system when a GLink request is fulfilled or rejected, with animations reacting accordingly.
The practical impact is immediate. Sharing a specific blockchain transaction with another user becomes a matter of copying a link. Pre-filling a payment form for a merchant takes one URL. Pointing someone to a specific block in the explorer requires no instructions — just a GLink. The Share button in the Blockchain Explorer UI dApp generates GLinks with a single click.
Hard Fork: On-Chain Transaction Metadata
This is the feature that necessitated the hard fork — and the reason 1.9.5 carries the “Hard Fork” designation. It is also one of those changes that sounds mundane on the surface but fundamentally reshapes how the entire system operates.
Before 1.9.5, determining what a transaction did required parsing its GridScript bytecode. GridScript is Turing-complete. Parsing Turing-complete code to extract metadata is slow, fragile, and fundamentally unbounded in complexity. The Blockchain Explorer had to guess what a transaction did by running a specialized parser that understood common patterns — and that parser was a maintenance burden that grew with every new GridScript command. Every time the team added a new instruction to the VM, the parser needed a corresponding update. It was technical debt with compound interest.
After 1.9.5, every transaction carries explicit metadata written during execution. The GridScript VM now sets flags and stores structured data in BER-encoded fast cache structures as it processes each instruction. No more guessing. No more parsing. The transaction tells you what it did:
- Transaction type (value transfer, identity registration, token pool deployment, off-chain cash-out, sacrifice, etc.)
- Per-recipient transfer amounts (accumulated across all
sendandsendExoperations) - Token Pool identifiers and Transmission Token details
- Bitflag-based type system — a single transaction can carry multiple type flags (e.g., both a transfer and a token pool deployment)
The new mkfilter GridScript command enables blockchain-wide search from pure GridScript — no JavaScript required. Create a search filter, push it onto the stack, invoke context -c searchBlockchain, and receive matching transactions in milliseconds. All Identity Token deployments. All off-chain cash-outs. All sacrificial transactions. Instantly.
The legacy GridScript parser has been retired for processed transactions, yielding measurable TPS throughput improvement. It is retained only for mempool transactions awaiting processing.
Phantom Leader Mode
On November 30, 2025, the Emergency Response Team detected what appeared to be a transaction-withholding attack on Live-Net. Key blocks were being produced, but transactions from mempools were not being confirmed. Three development tickets were immediately scheduled.
The response was not just a patch — it was a new capability: Phantom Leader Mode.
Any Operator can now simulate transaction processing as if they were the elected Proof-of-Work leader. The node forms a block, processes pending transactions, generates a full report — but never broadcasts the result to the network. It is a sandbox for consensus. Think of it as a flight simulator for block production: full fidelity, zero consequences.
chain -phantom onactivates the modechain -phantom reportdisplays full processing results including failed transaction analysis- Normal block processing and consensus participation are completely unaffected
Phantom Mode was instrumental in debugging the Token Pool deployment pipeline — confirming that invalid transactions would fail in Phantom Mode before they could reach consensus.
Additionally, the Vitals Monitoring sub-system was enhanced: a background thread now continuously monitors the oldest unprocessed transaction. If three or more key blocks pass without that transaction being processed, a warning is issued to all active Operators with a suggestion to activate Phantom Mode for investigation.
Three security mitigations were deployed in response to the suspected attack:
- Eliminated data-block formation disable functionality — the code path allowing Operators to produce key blocks without data blocks was removed entirely
- Closed Hard Fork mode loophole — an attacker could no longer claim to lead a hard fork while only producing key blocks
- Heartbeat mechanics for block formation threads — preventing external termination of block production
Decentralized User Interface (DUI) Enhancements
Building a fully decentralized user interface inside a browser tab — with no extensions, no native code, and no server-side rendering — means solving problems that most frontend teams never encounter. Every optimization that web frameworks take for granted (server-side hydration, native plugin access, multi-threaded rendering) has to be reinvented from first principles within the constraints of a single browser context. The DUI work in 1.9.5 reflects months of confronting those constraints head-on, and in several cases, turning them into architectural advantages.
- GRIDNET OS Curtain — a barely transparent overlay managed by the operating system to mask HTML rendering imperfections during Shadow DOM element updates. Called the “Venice Design Paradigm,” it was extended with a Whitelist API: UI dApp developers can now exempt specific DOM elements from curtain animation (essential for sliders and other interactive controls). Full documentation with 12 subsections added to the sample UI dApp template.
- Focus Management System — a complete system-wide focus management architecture:
CVMContexttracks system-level dialog activity,CWindowManagermaintains focused window state,CWindowprovidescanCaptureFocus()checks, and the Wallet PIN overlay respects focus permissions. No more windows hijacking keyboard input during system operations. - Process isolation — multiple instances of the same UI dApp running within a single browser tab with proper event isolation. Three simultaneous Wallet instances, each with different activated wallets, were tested with proper compartmentation.
- Web Workers integration — BER decoding and CPU-intensive object instantiation offloaded to dedicated Web Workers. This was described internally as “an extremely complicated change” — Web Workers strip ECMA6 objects of their class prototypes, requiring manual re-casting of plain JavaScript objects back to strongly typed interfaces.
- Performance optimization — elimination of 22–40 second UI freezes:
Promise.all()microtask explosions replaced with sequential loading and UI yielding; matrix animation frame rendering reduced from 314ms to sub-16ms; thumbnail generation given progressive thread yielding. - Key-chain API — operating system-level API providing keychain management, secure desktop prompts, and re-encryption capabilities to UI dApp developers.
- Unified Local/Remote Data Request Pipeline — streamlined data request mechanics behaving identically whether data is requested from a full node or local UI dApp instance.
- System-Wide UI dApp Data Request Tracking — full AAA-paradigm accountability with unique IDs, system-wide tracking, and asynchronous cleanup with configurable timeouts.
Security Enhancements
Security in a decentralized system does not get a dedicated sprint — it is woven into every feature, every protocol change, every line of code that touches keys, signatures, or network-facing surfaces. The enhancements below span the full stack, from in-browser cryptography to hardware-level encoding validation, and reflect a consistent principle: if a component handles sensitive data, it must be hardened independently, not rely on the layer above or below it for protection.
- ECC authentication from browser — private key signing performed entirely within the browser. When a QR Intent authentication request arrives from a remote Core node, the
CKeyChainManagerintercepts it and signs autonomously — backward-compatible with the existing QR authentication flow. The browser becomes a first-class authentication provider. - PBKDF2 PIN security — PIN values stored as salted hashes using PBKDF2 with random IV vectors. The old plaintext storage was identified, flagged, and replaced in a single development session.
- AES-GCM recipient encryption — stored recipients encrypted with PIN-derived keys (100,000 PBKDF2 iterations). Zero plaintext storage when wallet locked.
- Ephemeral security tokens — pre-authentication mechanics for domain operations without requiring full ECC-based strong authentication.
- Hardware encoding self-tests — obligatory self-tests during Core startup verify hardware-accelerated base64/check encoding against hard-coded reference values. Even when the CPU reports AVX-512/AVX2 support, computational results are compared to detect platform-specific encoding bugs.
- HTTP layer attack detection — two-tier architecture: Layer 1 (blacklisting) for attacker identification and logging, Layer 2 (sandbox escape detection) as hardened defense.
- In-Browser Threat Model Architecture — comprehensive threat model revision for the in-browser GRIDNET OS subsystem, modeling vectors including malicious UI dApps attempting private key capture and malicious nodes requesting signatures for arbitrary GridScript code.
- Visual C++ Runtime Deployment Hardening — multi-methodology approach ensuring proper VC++ Runtime availability across all operator environments.
- Build Validation Across Configurations — security module integration validated in both Release and Debug build modes across all 15+ GRIDNET Core sub-libraries.
- Compartmentalized Codebase Access Model — multi-library architecture where sub-teams work on isolated components, mitigating insider threat vectors.
AI-Augmented Development Pipeline
The 1.9.5 cycle marks a paradigm shift in how GRIDNET Core is developed. For the first time, Anthropic AI processing was integrated into the daily development workflow — not as an experiment, but as a load-bearing component of the engineering process.
The shift was born of necessity. The breadth of changes required — spanning C++ kernel code, JavaScript browser subsystems, GridScript compilers, BER serialization, ECC cryptography, and responsive CSS — would have taken a small team considerably longer without AI augmentation. But adopting AI as a development tool does not mean trusting it blindly. The workflow that emerged over this cycle is defined as much by its verification discipline as by its generation capability — every AI-produced artifact was reviewed by a human, on camera, before it touched the codebase.
How it was used:
- Root cause analysis — AI-aided diagnosis of promise resolution failures in ECMA6 async futures, protocol layer mismatches between GridScript response types, and detached VM thread architectural bottlenecks.
- Cross-platform compiler validation — AI agents autonomously compared C++ and JavaScript GridScript compiler outputs, implementing unit tests, correlating test vectors, and identifying discrepancies — treating the C++ implementation as the reference.
- Crash dump analysis — WinDbg crash dumps provided directly to AI agents for autonomous investigation, yielding positive results for identifying null-pointer dereferences and memory corruption patterns.
- Code generation with human validation — AI-assisted development of Wallet UI dApp features, with every line reviewed on YouTube LIVE. The human role shifted from writing code to reviewing code, validating architecture, and catching cases where AI attempted to bypass security checks (noted: “AI agents sometimes attempt to omit security validations as a path of least resistance”).
- Context preparation — systematic preparation of AI agent task contexts on YouTube LIVE, including architecture documentation, code snippets, and expected behaviors.
The result: a development workflow where approximately 75% of effort goes to testing and validation, and 25% goes to code generation. The AI writes; the human verifies. All on camera.
- AI-Aided Crash Dump Analysis — semi-automated analysis of LARS diagnostic reports accelerating root-cause identification; led directly to discovery of uninitialized constructor fields and unprotected variable access.
- AI-Assisted Market Making Research — AI engines employed for volatility-calculation algorithms, attack-detection heuristics, and strategy optimization.
- AI-Aided Security Audit — deployed internal AI cloud and Anthropic Opus 4 for offline analysis of compliance algorithms, identifying potential misplacement paths that could cause asset loss.
LARS System Overhaul
When a node crashes at 3 AM and nobody is watching, the only thing standing between a recoverable incident and a mystery is the quality of the crash dump that gets captured. LARS — the Liveness Assurance & Reporting Service — is GRIDNET’s crash dump collection and node monitoring system, and it is one of those invisible pieces of infrastructure that only gets attention when it fails. In this release, it failed — and that failure led to a complete overhaul that transformed LARS from a passive crash reporter into an autonomous node lifecycle manager.
The root cause was deceptively subtle: the procdump utility was configured with -e 1 (capture on first-chance exception), which caused it to dutifully dump the benign SEH validation test that runs at startup — and then exit, satisfied it had done its job. Minutes later, the actual fatal crash occurred with no one listening. The fix was straightforward once diagnosed: switch to second-chance (unhandled) exception capture only. But the investigation revealed how much more LARS needed to become, and the team took the opportunity to rebuild it into something far more capable.
Additional improvements:
- Live diagnostic dumps — Operators can now submit memory dumps of running GRIDNET Core instances (ad-hoc diagnostics, not just crash reports)
- Optimized dump sizes — switched from full process memory dumps (10+ GB) to mini-dumps (1–10 MB) collecting only stack frames, loaded DLLs, handles, and thread metadata
- New naming format —
GRIDNET Core.exe_YYMMDD_HHMMSS_HOSTNAME_TYPE.zipwith_LIVE.zipand_CRASH.zipsuffixes - Version reporting — LARS reports now include GRIDNET Core version, LARS version, and build metadata
A comprehensive security audit of all submitted crash dumps confirmed: loaded DLLs clean, memory patches clean, stack integrity clean, vtable integrity clean, heap corruption clean, shellcode clean, injected threads clean. Since September 8, 2025, only a single valid post-initialization crash dump was submitted.
The overhaul did not stop at better crash reporting. Once we had a reliable, always-running service sitting alongside every GRIDNET Core instance, the natural question became: what else should this service be responsible for? The answer turned out to be quite a lot.
- Autonomous Software Update Engine — LARS gained the ability to autonomously download, verify, uninstall, and install new GRIDNET Core versions without operator intervention, including version comparison against bootstrap nodes, graceful Core process termination with three fallback methods, silent MSI execution, and post-install re-launch.
- Custom MSI Installer Extension — a purpose-built DLL extension to Microsoft Installer launches LARS immediately upon installation, with security token manipulation via
WTSQueryUserTokenand fallback strategies including Task Scheduler registration. - Pre-Update Validation Suite — comprehensive pre-flight checks including storage space verification with wait-and-retry, JIT debugger disengagement, WER suppression, ProcDump termination, and singleton instance enforcement.
- Blockchain Height Stall Monitoring — advanced monitoring of GRIDNET Core operational parameters including blockchain height stall detection and scheduled restart functionality.
- Crash-Loop Resilience — LARS can now check for updates independently of whether GRIDNET Core is running, enabling autonomous recovery from crash-loop scenarios.
- GPU Diagnostic Integration — reports now include GPU information via OpenCL and DirectX fallback heuristics.
- Runtime DLL Introspection — LARS enumerates all loaded DLLs of a running GRIDNET Core process, detecting Visual C++ runtime versions and .NET frameworks.
- Autonomous VC++ Runtime Management — three-fold deployment approach: embedded VC++ installer, MSI-embedded module invocation, and private DLL fallback.
Operator & Developer Experience
A blockchain core can have the most elegant consensus algorithm ever designed, but if operators dread interacting with it and developers cannot debug it efficiently, none of that elegance matters. This release includes a collection of improvements — some large, some small — that came directly from the experience of running and developing against GRIDNET Core day after day. Every item here exists because someone hit a real friction point and decided to fix it properly.
-resetswitch — new command-line switch for clearing ERG settings.- GridScript command availability audit — comprehensive review ensuring correct availability of commands from Smart Contract context. Risky codeword sequences disabled in kernel-mode.
- Phantom Leader Mode — described above; a significant new tool for Operators investigating network behavior.
mkfilterand enhancedcontextcommand — blockchain search from the terminal. MAN pages updated with examples 22–25.- Header file restoration — recovery of two major header files accidentally unversioned from SVN.
- OpenCL device deduplication — NVIDIA RTX A2000 devices detected twice due to multi-platform driver registration now deduplicated via
CL_DEVICE_UUID_KHRextension. - Compiler diagnostic optimization —
#define COMPILER_DEBUG_MODE 0compiles out per-decompile diagnostic logging in production (zero overhead during sync).
Hard Fork Cross-Validation
A hard fork is the most dangerous operation in blockchain engineering. The state trie — the data structure encoding every account, every balance, every identity — must be byte-identical between the old and new versions at the fork point. A single bit of divergence means a consensus split.
Before this release, verifying that guarantee was a manual, nerve-wracking process that depended heavily on careful inspection and a healthy dose of faith. We decided that faith is not an engineering methodology. The 1.9.5 release introduces tooling that makes cross-validation systematic and repeatable — so that every future hard fork can be verified with the same rigor, by anyone, at any time.
chain -dump— dumps the complete state of all domains at any blockchain height into a JSON file. Format:VERSION_HEIGHT_state_dump.json. Includes core version, blockchain height, state perspective hash, total domains, total GNC balance, and a sorted array of all domains with address, balance, and nonce.chain -validate— loads dumps from different GRIDNET Core versions and performs automated cross-version comparison. Validates perspective match, total domain count, total GNC balance, and domain-by-domain address existence and balance equality. Outputs a colored pass/fail report.
The validation was performed on Tier 0 infrastructure: an AI agent created an SVN branch, back-ported the dump/validate commands to GRIDNET Core 1.9.4 (the current Live-Net version), compiled it, and deployed it to Tier 0 node 162.55.244.227. State was dumped at blockchain height 140864.
Result: ALL READINGS NOMINAL. Complete domain/balance/nonce consistency between GRIDNET Core 1.9.4 (Live-Net) and 1.9.5 (hard fork candidate).
This procedure is now mandatory for every future Hard Fork.
Blockchain Explorer Enhancements
The Blockchain Explorer started its life as an experimental prototype — a way to peek into on-chain data while the real infrastructure was being built. With this release, the experiment is over. The new on-chain metadata system introduced in 1.9.5 opened up possibilities that the original explorer was never designed to handle, so the team rebuilt it into something worthy of being the primary window into GRIDNET’s blockchain.
- Renamed from “Experimental Blockchain Explorer” to “Blockchain Explorer”
- Transaction-type filtering — instant search by type (identity deployments, sacrifices, token pool registrations, off-chain cash-outs) using the new metadata system
- SVG action icons — visual transaction type indicators
- View traversal — tapping Block ID navigates to block details, tapping Miner ID navigates to miner details
- Professional context menus — right-click with options to jump to issuer/block/recipient, copy any field, with glossy icon animations and cyberpunk scan-line effects
- GLink sharing — one-click URL generation to share specific transactions or blocks
- 3D animated transaction details — with foldable sections
Liquidius Maximus — In-House Market Making Engine
A comprehensive Python-based high-frequency trading and market-making platform was developed from the ground up to provide liquidity for the GNC/USDT pair on Xt.com. What began as a basic spread-maintenance tool evolved over six months into a sophisticated multi-strategy engine with real-time attack detection, autonomous defense mechanisms, and advanced volatility modeling.
Open Source Commitment — Following the decision to terminate cooperation with Xt.com due to their predatory market practices (see Exchange Interaction & Market Integrity below), the GRIDNET project has committed to releasing the entire Liquidius Maximus platform as open source. The codebase — including all trading strategies, attack detection algorithms, volatility models, compliance mechanisms, and the Qt6 profiling/visualization tooling — will be made publicly available, enabling the broader community to audit, extend, and deploy the engine on any exchange. This represents one of the most comprehensive open-source market-making platforms ever released, encompassing over six months of continuous development streamed publicly on YouTube LIVE.
The scope of what was built here deserves a moment of context. Market making on a centralized exchange — especially for a low-liquidity pair on an exchange that, as we later discovered, was actively working against us — is not a problem you solve with a single algorithm. It is an arms race. Every strategy we deployed was met with new forms of hostile behavior, which demanded new detection systems, which revealed new attack vectors, which required new defenses. The result is a platform that grew organically from necessity, each component forged in response to a real, observed threat. Every feature listed below exists because something on the other side of the order book forced us to build it.
- Multi-Strategy Architecture — over 20 market-making strategies ranging from basic symmetric spread placement and inventory balancing through to advanced approaches employing fractal-based support/resistance level detection, volatility-based positioning, market trend following, and AI/regression-aided spread optimization with dynamic repositioning based on market velocity and direction.
- Custom Qt6 Performance Profiler — in-house Python profiling and visualization engine featuring interactive flame charts with nested call-relationship preservation, pie-chart time-distribution views, hover-based legends, and panning/scaling controls. Used to pinpoint SSL/TLS transport overhead as the dominant latency factor and eliminate mutex congestion bottlenecks (reducing lock contention from 200ms to sub-millisecond). This tool was not planned from the start — it was built because we needed to understand why certain operations were orders of magnitude slower than they should have been, and no existing profiler gave us the granularity we needed.
- Sandwich & Pump-and-Dump Detection Engine — multi-signal attack detection system using six heuristic factors: rapid pump detection, volume spike analysis, price velocity measurement, order book thickness assessment, spread anomaly detection, and order book imbalance scoring. Composite confidence scores classify attack severity into tiered categories with autonomous mitigation: halting buy-side requoting, calculating precise GNC dump quantities, executing neutralization orders, and restricting order placement during cooldown.
- Self-Learning Defense Adaptation — the sandwich-attack recognition module autonomously improves its detection parameters based on collected data and past mitigation outcomes, with detected events enqueued for global statistical analysis and parameter adjustment. In practice, this means the system gets harder to exploit with every attack it observes.
- Garman-Klass-Yang-Zhang Volatility Estimation — advanced multi-factor volatility calculation incorporating exponentially-weighted realized volatility, active-period filtering, jump-component analysis for high-frequency attacks, microstructure noise estimation, and gap-risk assessment. Combines 1-minute and 1-hour kline data using mathematical fusion techniques.
- Flashing Order Book Module — multi-threaded flashing-order-book sub-system with configurable per-order appearance and disappearance intervals, autonomous market-movement sensing for safety cancellation, and anti-flash order detection for hostile buy-side depth manipulation.
- Internal Simulation Engine — advanced simulation engine for simulated order matchmaking, enabling offline evaluation and AI-aided analysis of all trading strategies prior to live deployment. Every strategy runs through this simulator before it touches real capital — a discipline that saved us from deploying approaches that looked promising in theory but would have hemorrhaged funds in the adversarial conditions we were operating in.
- Private WebSocket Low-Latency Feed — dedicated private WebSocket communication link to Xt.com for real-time order, trade, and balance-change notifications with bootstrap via RESTful historical backfill.
- GTX (Post-Only) Order Placement — switched from GTC to GTX mode, guaranteeing orders cannot be filled at placement time, enabling precise measurement of placement-to-execution delay for forensic detection of hostile front-running. This seemingly small change proved to be one of the most important forensic decisions in the entire project — by ensuring our orders could never be immediately filled, we created a clean measurement baseline that made front-running activity unambiguously detectable.
- Idempotent & Stateless Compliance Architecture — all compliance algorithms (spread assurance, price-gap mitigation, near-depth/total-depth assurance) designed to be both idempotent and stateless, independently toggleable via UI for compartmentalized evaluation.
- Dense Price-Gap Mitigation — optional mode structuring the first 20 orders on both sides as tightly as possible near best bid/ask, minimizing price fluctuation in illiquid conditions.
- Stop-Loss, Rebalancing & Circuit Breaker — dual-mode rebalancing (market acquisition vs. self-wash-trading for illiquid conditions), configurable circuit-breaker thresholds, and persistent risk-management configuration.
- Comprehensive Report Generation — CSV, JSON, and PDF export with sortable/filterable order-history views featuring autonomous safety-score assessment based on fill latency.
Network Connection Management
A decentralized network is only as strong as its ability to maintain connections under adversarial conditions. In the real world, GRIDNET Core nodes face everything from aggressive peers attempting to exhaust connection slots, to DDoS attacks aimed at isolating nodes from the network, to the quieter but equally damaging problem of NAT traversal failures and packet loss on mobile networks. This release represents a comprehensive hardening of the connection management layer — the result of observing how the network behaves under genuine stress on Live-Net and systematically closing every weakness we found.
- Per-IP Connection Throttling — connection management revised with per-protocol-type bucket counters on incoming connection attempts, hardware resource availability verification, and time-window-based throttling to prevent connection exhaustion from aggressive peers.
- Low-Connectivity Fallback Mode — fallback mechanism that activates when peer connectivity drops below acceptable thresholds, temporarily relaxing per-IP connection windows to allow re-establishment of network presence. The reasoning here is straightforward: when you are nearly disconnected from the network, accepting connections you would normally throttle is better than remaining isolated.
- Autonomous Kernel-Mode Firewall Integration — anti-DDoS mechanics tightened with improved integration with Windows kernel-mode firewall rules, including proper timestamp comparison fixes and synchronization cleanup for firewall rule lifecycle management.
- Kademlia Thread Management — improved thread management around the Kademlia peer discovery protocol, including proper cleanup of discovery threads and fixes for timestamp comparison inaccuracies.
- QUIC Transport Layer Keep-Alive Tuning — QUIC keep-alive intervals adjusted to better cope with selective routers, with the beneficial side effect of improving mobile application connectivity. Some routers aggressively drop QUIC sessions that appear idle — tuning the keep-alive cadence keeps these connections alive without generating excessive overhead.
- Application-Layer & Transport-Layer Ping Synergy — data exchange mechanics adjusted to benefit from both application-layer and QUIC transport-layer ping-alive mechanics, yielding more stable connections in networks with massive packet loss or behind NATs.
- Maximum Data Package Size Extension — maximum data package size extended from 40 MB to 200 MB to accommodate growing blockchain length during Genesis-to-head synchronization. As the chain grows, so does the data volume required to bring a new node up to speed — this five-fold increase ensures that synchronization remains viable as the blockchain matures.
- Block Availability Confidence Levels — boolean block-availability checks replaced with confidence-level assessments, accounting for scenarios where a remote node advertises a leading block whose chain-proof has not yet been locally verified. This is a subtle but important change: the old binary model — “the block exists or it does not” — could not express the nuance of “the block has been announced but not yet proven,” which led to unnecessary re-fetches and synchronization stalls.
Exchange Interaction & Market Integrity
What follows is a factual record of our experience operating on Xt.com, documented through months of forensic data collection by the Liquidius Maximus platform. We present these findings not with anger but with the precision they deserve — because the evidence speaks for itself, and because other projects listing on centralized exchanges need to know what they may be walking into.
- Xt.com API Anomaly Investigation — investigated and documented multiple anomalous behaviors from Xt.com: CloudFront 403 rejections below documented API limits, unexplained order cancellations with no reason given, and suspected exchange-side front-running. Market services halted upon detecting unusual behavior, with forensic analysis and detailed evidence reported to Xt.com.
- Exchange Compliance Feasibility Assessment — multi-week evaluation of feasibility of upholding market-making requirements on Xt.com GNC/USDT pair, assessing order rejection patterns and volume assurance failures.
- Volume Assurance & Anti-Front-Running — ACID self-trade volume assurance with hysteresis-based stability checks: SELL LIMIT orders placed first (GTX), verified stable for ~2 seconds against hostile bot consumption, then consumed if untouched. Detected and documented front-running events (12.5 USDT in 9 hours of operation).
- Systematic Exchange-Side Front-Running & Market Manipulation — forensic analysis conducted over multiple months revealed a persistent pattern of exchange-side predatory behavior by Xt.com that had been ongoing since the GNC token listing. Evidence collected by the Liquidius Maximus profiling and detection systems documented: (1) consistent front-running of placed orders with sub-millisecond reaction times achievable only with exchange-side order-book visibility, (2) coordinated pump-and-dump cycles targeting GNC liquidity, and (3) API throttling and order rejection patterns that selectively disadvantaged the market maker while permitting hostile bot activity. The totality of evidence points to Xt.com operating in direct conflict with the interests of listed projects.
- Termination of Xt.com Cooperation & Legal Action — based on the accumulated forensic evidence of predatory market practices, the GRIDNET project made the decision to terminate all cooperation with Xt.com. Legal proceedings are being prepared to address the documented market manipulation. A budget exceeding 1,000,000 USDT has been allocated for cross-chain integration with Hyperliquid, a decentralized exchange where order matching occurs on-chain without the possibility of exchange-side front-running. The entire Liquidius Maximus market-making engine will be open-sourced as part of this transition.
Xt.com Exchange — Forensic Investigation & Warning to Listed Projects
What follows is one of the most difficult sections we have ever had to write. Not because the evidence was hard to find — it was overwhelming — but because we did not want to believe what it was telling us.
When GRIDNET first listed GNC on Xt.com in April 2025, the team approached the partnership with genuine optimism. This was our first major exchange listing. We had spent weeks preparing the integration, invested over 35,000 USDT in listing and integration fees alone, and built an in-house market-making engine — Liquidius Maximus — from the ground up to provide fair, transparent liquidity for the GNC/USDT pair. Every line of its development was streamed publicly on YouTube LIVE, for the world to see.
We wanted it to work. We wanted Xt.com to be what it presented itself as — a reputable top-20 exchange where our token could find genuine price discovery and where our community could trade with confidence. For months, every time the data pointed toward something disturbing, we looked for alternative explanations. Every anomalous fill, every suspicious timing pattern, every inexplicable order cancellation — we asked ourselves: Could this be a bug in our code? Could this be a legitimate trader? Could there be an innocent explanation?
We built measurement tools. We built forensic profilers. We built fill-latency analyzers, sandwich-attack detectors, pump-and-dump classifiers, order-book manipulation sensors, and front-running counters. We did not build these tools because we wanted to find wrongdoing — we built them because we needed to understand what was happening to our market-making accounts, which were hemorrhaging assets at rates that defied every model we could construct.
And at every stage, the mathematics led to the same conclusion. The measurements pointed in one direction. The statistics permitted no alternative interpretation. Xt.com was not merely failing to protect the GNC listing — entities operating with exchange-level access to the order book were systematically extracting value from our market-making operations through front-running, pump-and-dump cycles, and interception of orders that should have been physically impossible for any external party to reach.
We say this with the weight of over six months of continuous forensic data collection, hundreds of thousands of logged events, and the professional judgment of developers who spent the majority of that period — what should have been spent on GRIDNET Core development — instead building increasingly sophisticated detection and defense mechanisms just to survive on a single exchange.
The Forensic Toolchain Built into Liquidius Maximus
The overwhelming majority of Liquidius Maximus development time was ultimately spent not on market-making strategies, but on building forensic instrumentation to understand, document, and defend against hostile activity. What began as a market-making engine evolved into what may be one of the most comprehensive exchange-forensics platforms ever built by a listed project. The forensic capabilities include:
- Fill-Latency Measurement System — every order placed on Xt.com was timestamped at placement and again at first fill notification. The delta between these timestamps, using Xt.com’s own API-reported values (not our local clock), formed the evidentiary basis for proving physically impossible fill speeds. Orders were autonomously classified by safety score based on fill latency.
- GTX (Post-Only) Forensic Mode — all orders switched from GTC to GTX placement mode, which the exchange guarantees will not fill at placement time. This eliminated the possibility that anomalous fills were artifacts of immediate matching, and enabled precise measurement of placement-to-first-fill delay for every order.
- Flashing Order Book with Randomized Timing — orders were displayed for configurable intervals (as low as 50ms) and hidden for longer periods (700–1200ms), with 30% random variance applied to both show and hide durations. This created a statistically testable framework: any entity achieving 100% snipe accuracy on randomized-timing orders with zero misses was, by definition, operating with advance knowledge of order placement.
- Sandwich & Pump-and-Dump Detection Engine — a six-factor heuristic system computing composite confidence scores from rapid pump detection, volume spike analysis, price velocity measurement, order book thickness assessment, spread anomaly detection, and order book imbalance scoring. Attack events were classified into severity tiers with autonomous mitigation: halting buy-side requoting, calculating precise dump quantities, and executing neutralization orders.
- MarketPressureSensor — real-time estimation of hostile bot GNC holdings at any given moment, including dump timing prediction based on observed accumulation patterns.
- ACID Self-Trade Monitor — a dedicated subsystem tracking the integrity of self-trade compliance orders. Every self-trade attempt was logged with: (a) timestamp of SELL LIMIT placement, (b) stability check duration, (c) whether the order survived to Phase 2, (d) whether the matching BUY executed successfully, and (e) if intercepted, the fill latency and quantity taken by the hostile entity. A front-running counter tracked every interception event.
- Match Explorer — forensic order-to-trade correlation tool enabling precise identification of which public trades matched which private orders, with timestamp comparison across Xt.com’s public and private API feeds.
- Comprehensive Report Generation — CSV, JSON, and PDF export with sortable/filterable order-history views, autonomous safety-score assessment, and complete trading history documentation. One such automated report covering the full GNC/USDT trading history at Xt.com is attached to this release.
Chronological Timeline of Key Forensic Findings
The following timeline documents the progression from initial suspicion to mathematical certainty. All timestamps are derived from contemporaneous development logs maintained in the LIVE-DEVELOPMENT Discord channel and corroborated by YouTube LIVE recordings.
April–May 2025 — Infrastructure Attacks Coincide with Listing
The hostile activity began before the first trade was even placed. On the same day the Xt.com listing timeline was announced (April 8), GRIDNET nodes came under targeted attack using deliberately malformed GridScript payloads. The Emergency Response Team was activated on April 9 when coordinated attacks hit multiple nodes. Attacks resumed on April 14 — three days before the expected listing go-live date — specifically targeting the metadata generation system that exchanges depend on for transaction processing. On May 6, a network black-hole attack capable of isolating nodes was discovered, and on May 21, a live Kademlia exploit using spoofed ICMP messages was detected (source IP: 2.27.211.165). By May 22, the development team was openly referring to the attackers as “enemies.”
May 12, 2025 — First Market Manipulation Evidence
The Emergency Response Team was activated to investigate a suspected attack designed to manipulate market-making services by injecting transactions with extremely small values near the mid-price. This forced the creation of an entirely new distinction between “Real Spread” and “Reported Spread” — the micro-orders were distorting the apparent spread to mislead the market-making algorithms. The development team documented “ongoing attempts to disrupt its operations” with “extremely small volumes right next to current mid-price” on the Xt.com GNC/USDT pair.
July 5, 2025 — Sandwich Attacks Confirmed on Xt.com
First explicit documentation of hostile bot activity: sandwich attacks and pump-and-dump operations targeting GNC market-making services. The attacks were sophisticated enough to require AI-based self-learning countermeasures.
July 9, 2025 — Xt.com’s Own Rules Enable the Exploitation
A critical realization: “The market making rules enforced by XT literally create a perfect environment for bot operators.” The requirement to maintain order book depth on both sides of the market at all times forced the market maker to constantly expose buy-side liquidity, which hostile bots then systematically exploited through pump-and-dump cycles.
July 12, 2025 — $400 USDT Loss per 15 Minutes Documented
Financial losses reached $400 USDT per 15 minutes ($1,600/hour) due to hostile bot activity causing 50% price waves. The hostile bots had not been deactivated — their amplitude had increased.
July 15, 2025 — The Exchange Itself Suspected
The first direct statement of what the data had been suggesting: “That is under the assumption that the attacker / bot operator is not the exchange itself (thus having access to information at no time delays and capable of acting at no time delays).” The team’s defense strategy worked against any external attacker — but not against an entity with zero-latency access to the order book.
July 30, 2025 — “Should a Project Require PhD-Level HFT Specialists?”
After weeks of building military-grade defenses, the team posed the question that captured the absurdity of the situation: “Should a project require PHD level high frequency trading specialists and developers to defend itself when entering a market?” The hostile conditions on Xt.com were so extreme that ordinary market-making services ($2–3K/month) would have been completely unable to survive.
August 3, 2025 — API Rate Limiting Below Documented Thresholds
CloudFront 403 rejections began occurring well below Xt.com’s documented API limits, selectively disadvantaging the market maker. For a market maker, having order placement blocked while existing orders remain live creates catastrophic exposure.
August 21, 2025 — The 70ms Fill: Physical Impossibility Proven
The forensic measurement system captured the evidence that would prove exchange-level access beyond reasonable doubt. A SELL limit order was filled within 70 milliseconds of placement — and that was not us who filled it. At 70ms, this fill occurred faster than Xt.com’s own WebSocket could disseminate order information to external parties. The team’s own software, placing an order and immediately filling it within the same function, could not achieve better than 120–170ms. A 70ms fill by an external party was, in the team’s words, a physical impossibility: “THERE IS NO OTHER POSSIBILITY.”
August 24–25, 2025 — 100,000 GNC Evaporated in 24 Hours
During a comprehensive live test with all protections active (orders flashed for 50ms, hidden for 700ms), approximately 100,000 GNC evaporated from market-making accounts in less than 24 hours. 39,000 GNC were lost in the first 1 hour and 26 minutes alone. Orders were being sniped at 90–300ms. Xt.com had previously claimed that only GRIDNET had API access to the GNC pair and that these were “human traders using the user interface” — at 150ms fill speeds.
September 18, 2025 — Self-Trade Front-Running: The Smoking Gun
The ACID self-trade mechanism — designed to place a SELL LIMIT order and then immediately fill it with a matching BUY to maintain volume compliance — was directly intercepted. A volume compliance SELL order was placed; 53% of it was filled by an unknown entity before the next line of Python code could execute the matching MARKET BUY. The system’s stability check caught it: “the order was filled SOONER than our software managed to fill it on its own few lines later… it is all rigged as FUCK.” The hostile entity then dumped the accumulated GNC, confirming the accumulate-and-dump pattern.
September 22, 2025 — 100% Snipe Accuracy on Randomized Orders
Orders configured with randomized timing (200ms show ± 30% variance, 1200ms hide ± 30% variance) were being sniped at 100% accuracy with zero misses, on a trading pair with virtually no other activity. This statistical impossibility — achieving perfect accuracy against randomized parameters with no background noise — constitutes near-certain proof of advance knowledge of order placement timing and parameters. Xt.com’s position: “these are all human traders.”
September 28, 2025 — Front-Running Counter Implemented
The development team built a dedicated front-running counter to track every interception event: "so that we know exactly how many times they’ve attempted to f** us."* The team explicitly concluded: “hostile bot is having privileged access to information (as it seems it does).” The self-trade mechanism was upgraded from MARKET to LIMIT orders in Phase 2 to prevent buying at front-runner-inflated prices.
September 30, 2025 — Even Atomic Batch Orders Compromised
In a final attempt to achieve atomicity, both sides of the self-trade were submitted as a single batch API call, expecting the exchange’s internal matching engine to process them as an atomic unit. The result: “believe it or not — even under these extreme conditions — the Xt.com internal order matching engine managed to mangle with 7 out of 117 self-trade attempts.” Even with spread assurance disabled and only atomic batch self-trades running, approximately $20 was extracted over 2 hours. The 1–10ms fill times on these orders were achievable only by an entity co-located with or operating within the matching engine itself.
October 7, 2025 — Exchange Cancels Orders Without Explanation
Xt.com unilaterally cancelled both sides of an ACID self-trade pair without providing any reason. In a separate 9-hour monitoring session: “there was only one event when Xt.com chose to front run one of our orders for 12.5 USDT” — note the attribution directly to Xt.com, not to a third party.
November 2025–February 2026 — Cessation and Migration
By November 2025, Xt.com was openly referred to as a hostile adversary. By December, the strategic decision was made to migrate to Hyperliquid, a decentralized exchange where order matching occurs on-chain — "where all those f*** cannot get us."* By January 2026, the assessment was final: Xt.com was described as a “scammy exchange” and the GNC price as drifting “at the bottoms of oblivion” — a price that the totality of evidence suggests was never a reflection of genuine market dynamics.
The ACID Self-Trade: How Exchange-Internal Front-Running Was Proven
The ACID (Atomicity, Consistency, Isolation, Durability) self-trade mechanism deserves detailed explanation, as it represents both the most sophisticated compliance tool built into Liquidius Maximus and the mechanism through which exchange-level front-running was conclusively proven.
Purpose: Xt.com’s listing agreement required minimum 24-hour trading volume and daily transaction counts. In the absence of organic trading activity (which was virtually nonexistent on the GNC pair beyond the hostile bot), Liquidius Maximus maintained compliance by trading with itself — placing coordinated buy and sell orders that would match each other.
Phase 1 (Pre-September 2025): A SELL LIMIT order was placed in GTX (post-only) mode. The system then waited approximately 2 seconds, verifying the order remained untouched — a stability check against hostile consumption. If stable, a matching MARKET BUY was executed to consume it. This had a known race condition: the hostile entity could intercept the SELL order during the stability window.
Phase 2 (Late September 2025): After documenting persistent front-running of Phase 1, the matching order was changed from MARKET to LIMIT — specifying exact price and quantity so that if the original SELL was no longer there (consumed by the front-runner), the LIMIT BUY would simply not execute, avoiding purchase at an inflated price.
Phase 3 (Late September–October 2025): Both orders were submitted as a single batch API call — an ephemeral SELL in GTX mode and a matching BUY in GTC mode — expecting the exchange’s internal matching engine to process them atomically. Even this was compromised: 7 of 117 attempts (6%) were interfered with at the matching engine level.
The Evidence Chain:
- Orders filled at 70ms when the API round-trip minimum was 120–170ms — physically impossible for any external party
- 100% snipe accuracy on orders with randomized 200ms/1200ms timing with zero misses — statistically impossible without pre-knowledge
- Self-trade SELL orders filled before the matching BUY could execute in the next line of Python code — direct interception
- Atomic batch self-trades compromised at the matching engine level — can only occur exchange-internally
- No trading activity without market-making enabled; instant hostile activity upon resumption — real-time awareness of market-maker state
- Xt.com claiming only GRIDNET had API access — if true, the hostile entity can only be exchange-internal
- Xt.com cancelling order pairs without explanation — direct exchange intervention
Financial Damages
| Category | Amount | Source Date |
|---|---|---|
| Integration & listing fees | 35,000 USDT | April 2025 |
| Total listing costs (incl. MM fees) | 100,000 USDT | September 2025 |
| Liquidius Maximus development costs | 350,000+ USDT | April–October 2025 |
| GNC balance drain (single test) | 39,000 GNC in 1h 26min | August 24, 2025 |
| GNC evaporated (24-hour period) | ~100,000 GNC | August 25, 2025 |
| Documented loss rate | $400 USDT per 15 minutes | July 12, 2025 |
| Micro-theft under atomic mode | ~$20 per 2 hours | September 30, 2025 |
The total financial impact exceeds 450,000 USDT in direct costs — integration fees that purchased access to a hostile trading environment, and six months of intensive software development that should never have been necessary.
Warning to Other Projects Considering Xt.com
We publish this forensic record not merely for our own documentation but as a warning to other blockchain projects, token teams, and market makers. The pattern we documented — where a project invests significant capital in listing fees only to discover that far more is subsequently lost through predatory exchange-side activity draining market-making accounts — may not be unique to GRIDNET.
Projects that raise funds for exchange integration with Xt.com should be aware that:
- Our 35,000 USDT in integration fees purchased access to a trading environment where entities operating with apparent exchange-level access systematically extracted value from our market-making operations
- The financial losses from predatory activity vastly exceeded the initial listing investment — what was spent on integration fees was dwarfed by what was effectively stolen from our market-making accounts through front-running, pump-and-dump cycles, and order interception
- Xt.com’s market-making requirements (maintaining both-side order book depth at all times) structurally enable exploitation by creating permanent liquidity targets that hostile actors can drain
- Formal complaints filed with Xt.com were either ignored or met with explanations (e.g., “human traders using the user interface”) that were physically contradicted by measured fill latencies
- The hostile activity was present from the first day of listing and persisted throughout the entire period of cooperation
- The level of technical sophistication required to merely survive on the exchange — PhD-level high-frequency trading expertise, custom forensic tooling, AI-based attack detection — is far beyond what any ordinary listed project or third-party market maker could reasonably provide
We ceased all cooperation with Xt.com and disabled all market making on the GNC pair. Legal proceedings are being prepared. The entire Liquidius Maximus codebase, including all forensic tooling, will be released as open source — so that any project can deploy the same measurement and detection capabilities we built and verify exchange behavior for themselves. A full automated trading history report generated by Liquidius Maximus covering the complete GNC/USDT trading history at Xt.com is attached to this release, documenting every order, every fill, every anomalous event.
The GRIDNET project has allocated a budget exceeding 1,000,000 USDT for cross-chain integration with Hyperliquid, a decentralized exchange where order matching occurs transparently on-chain — where the kind of exchange-internal manipulation documented here is structurally impossible.
Final Polishing
- Improved UI element positioning across all responsive breakpoints
- Dynamic scroll behavior for sub-identity tiles (maximum two rows visible)
- Transaction details view with foldable Source Code and Details panes
- Rate limiting for UI notifications
- Proper handling of virgin identity notifications
- Front-running detection improvements in market making software components
- Triple-ring cyberpunk loading animation with central lightning bolt
- Nickname input field dark-theme fix (resolved white background on focus)
- Sacrifice transaction polling fix (status codes 100-199 now correctly recognized as pending)
- Scrollbar styling aligned with cyberpunk theme
- Fork-out metadata cache bug fix preventing false “Forked Out” transaction reports